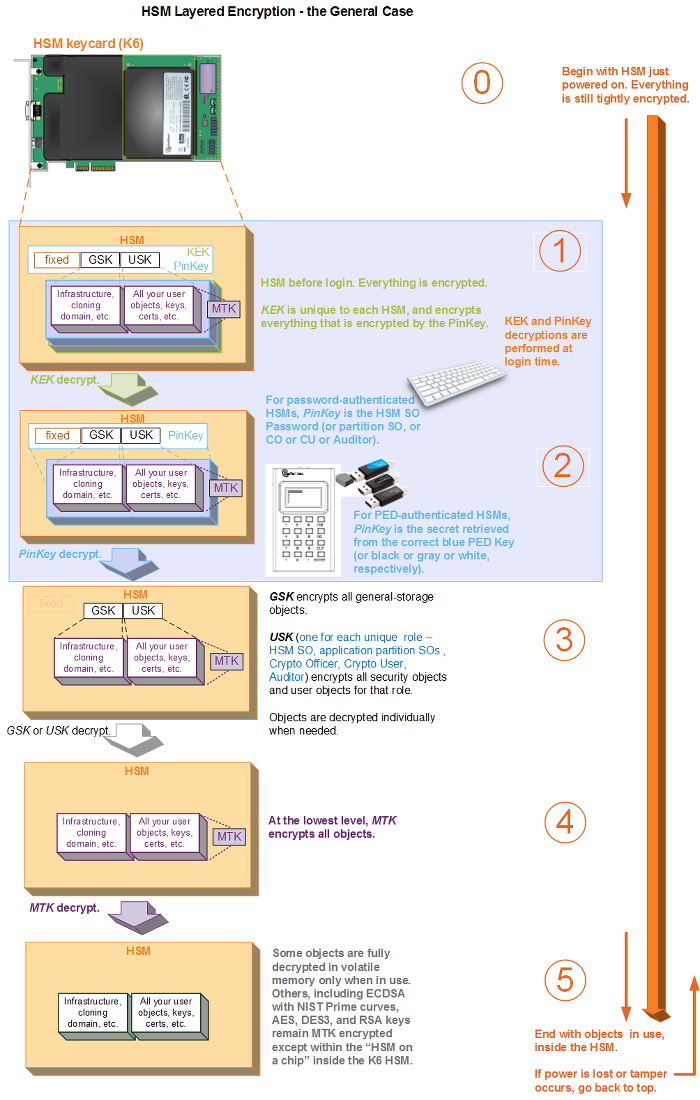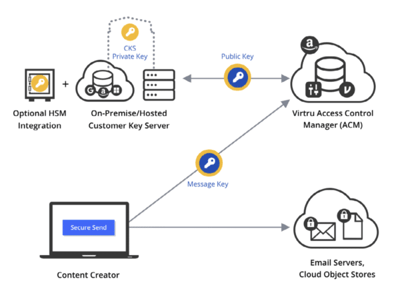
Encrypting Your Keys to the Cloud: Evaluating Microsoft 365 Double Key Encryption + HSM and Virtru + Google - Virtru

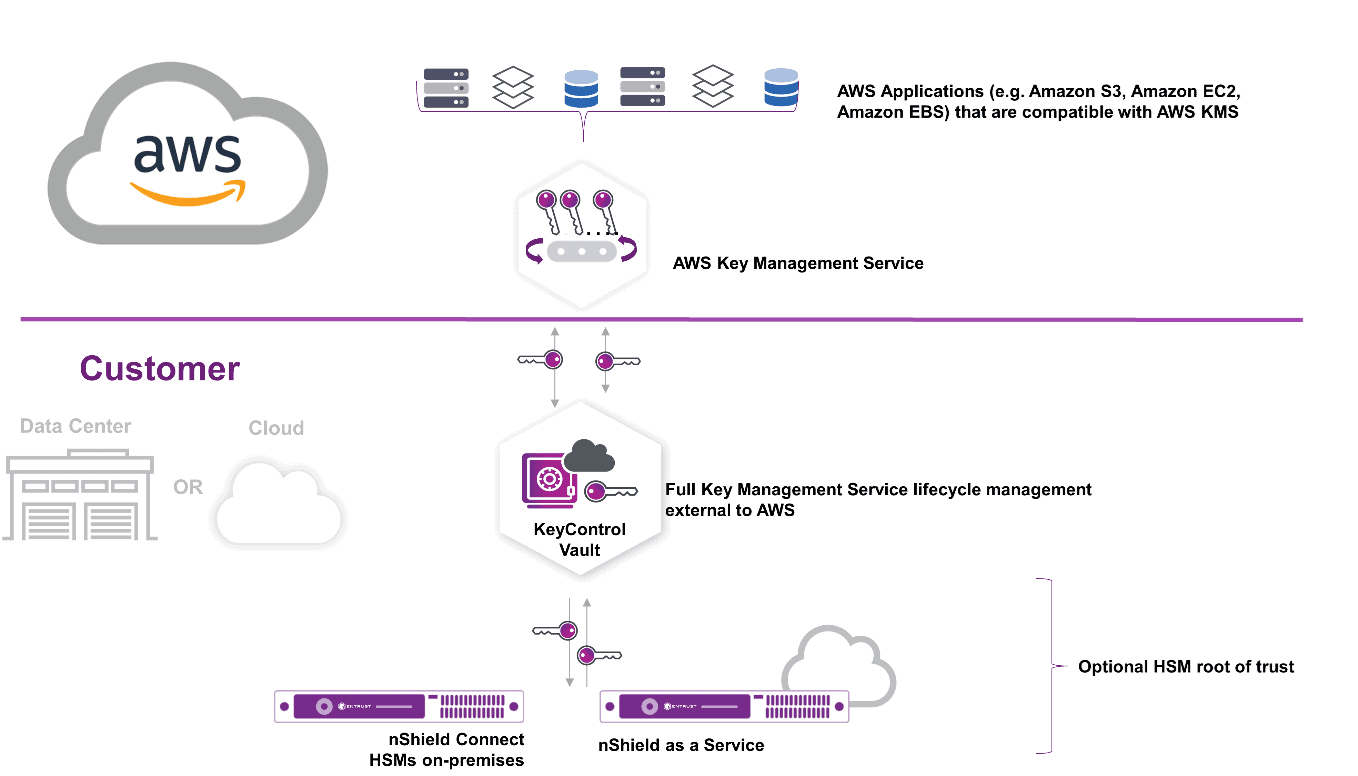
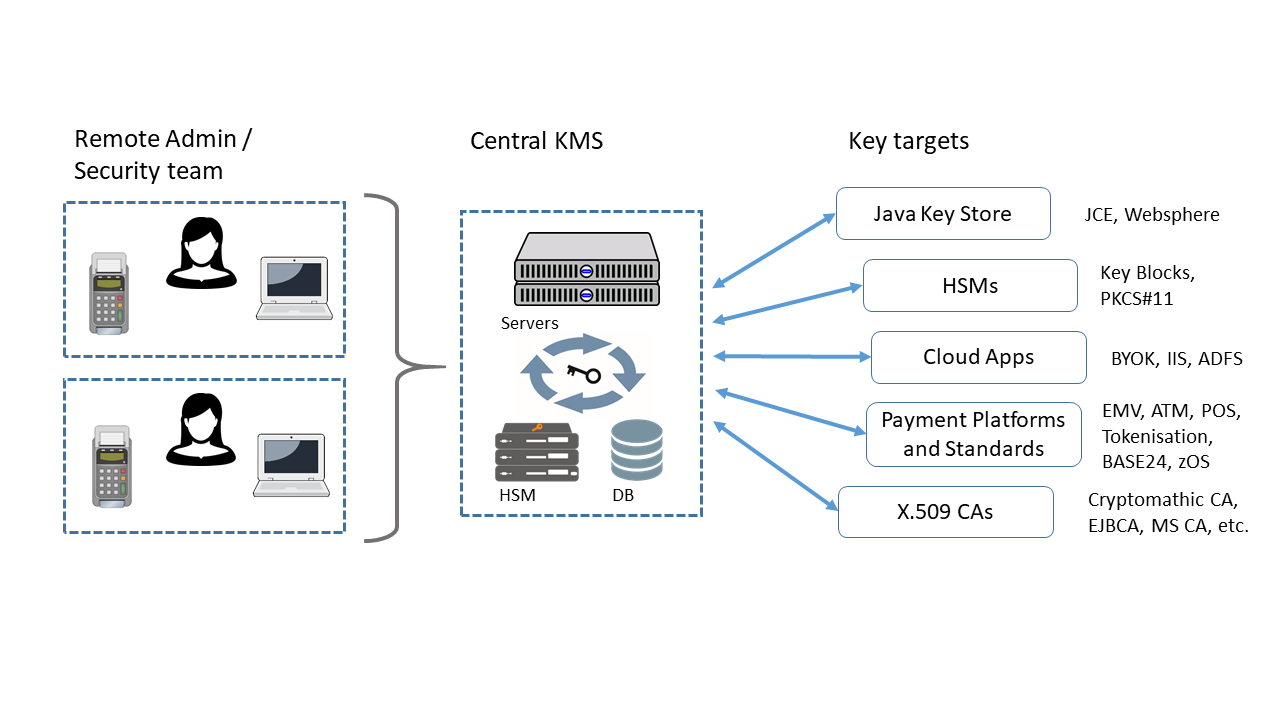
Demystifying KMS keys operations, bring your own key (BYOK), custom key store, and ciphertext portability | AWS Security Blog
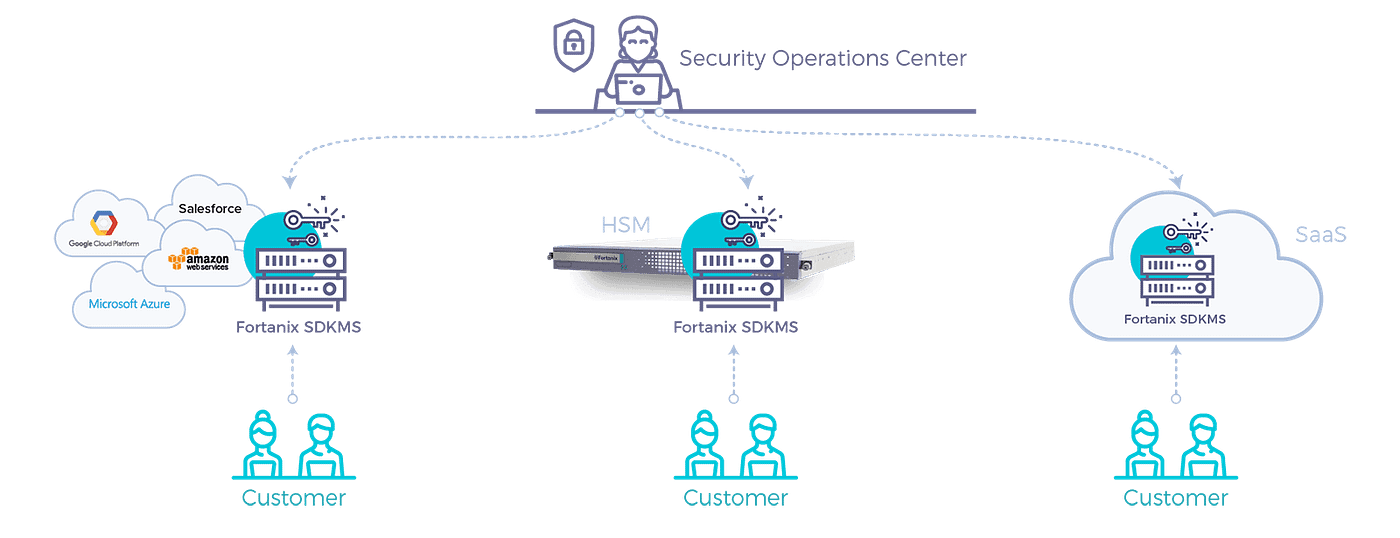
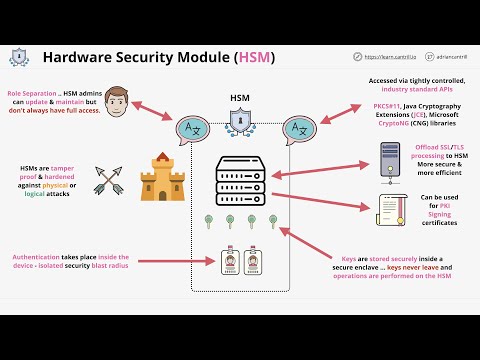
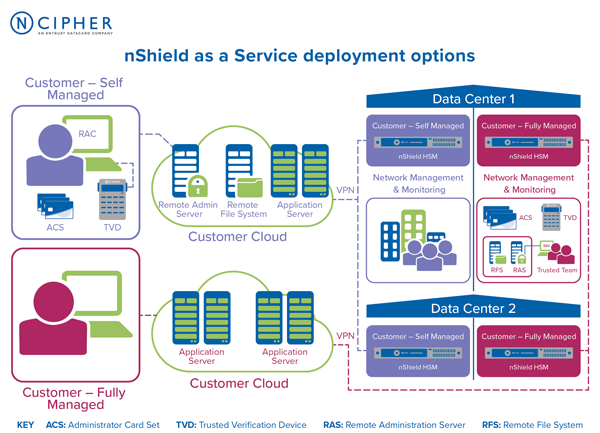
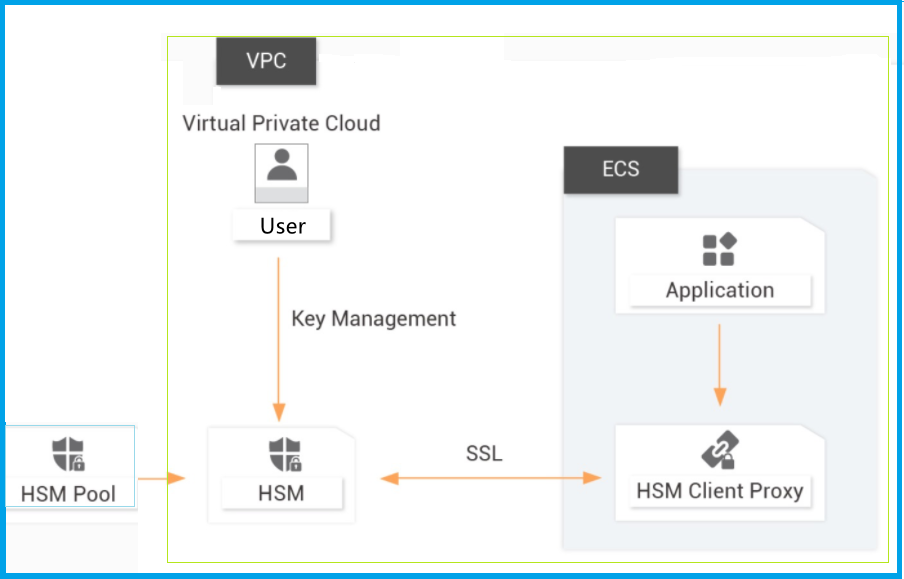
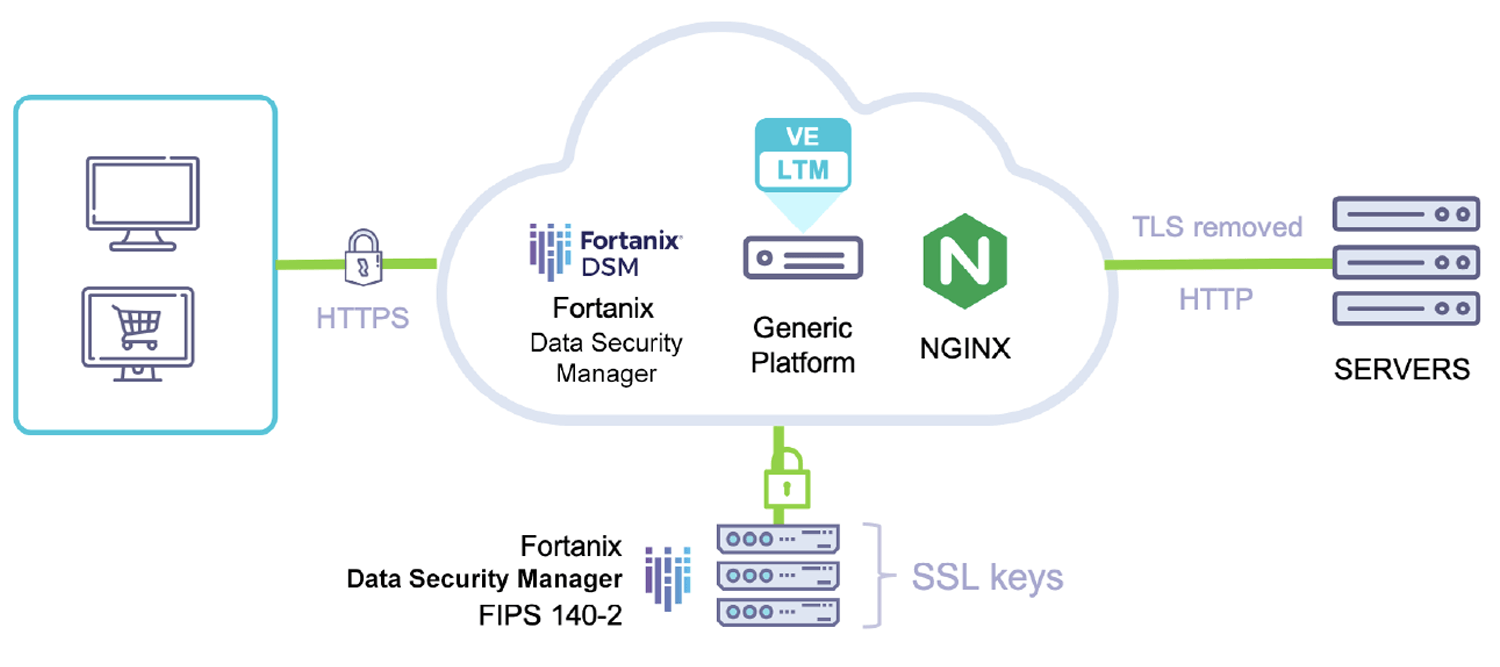
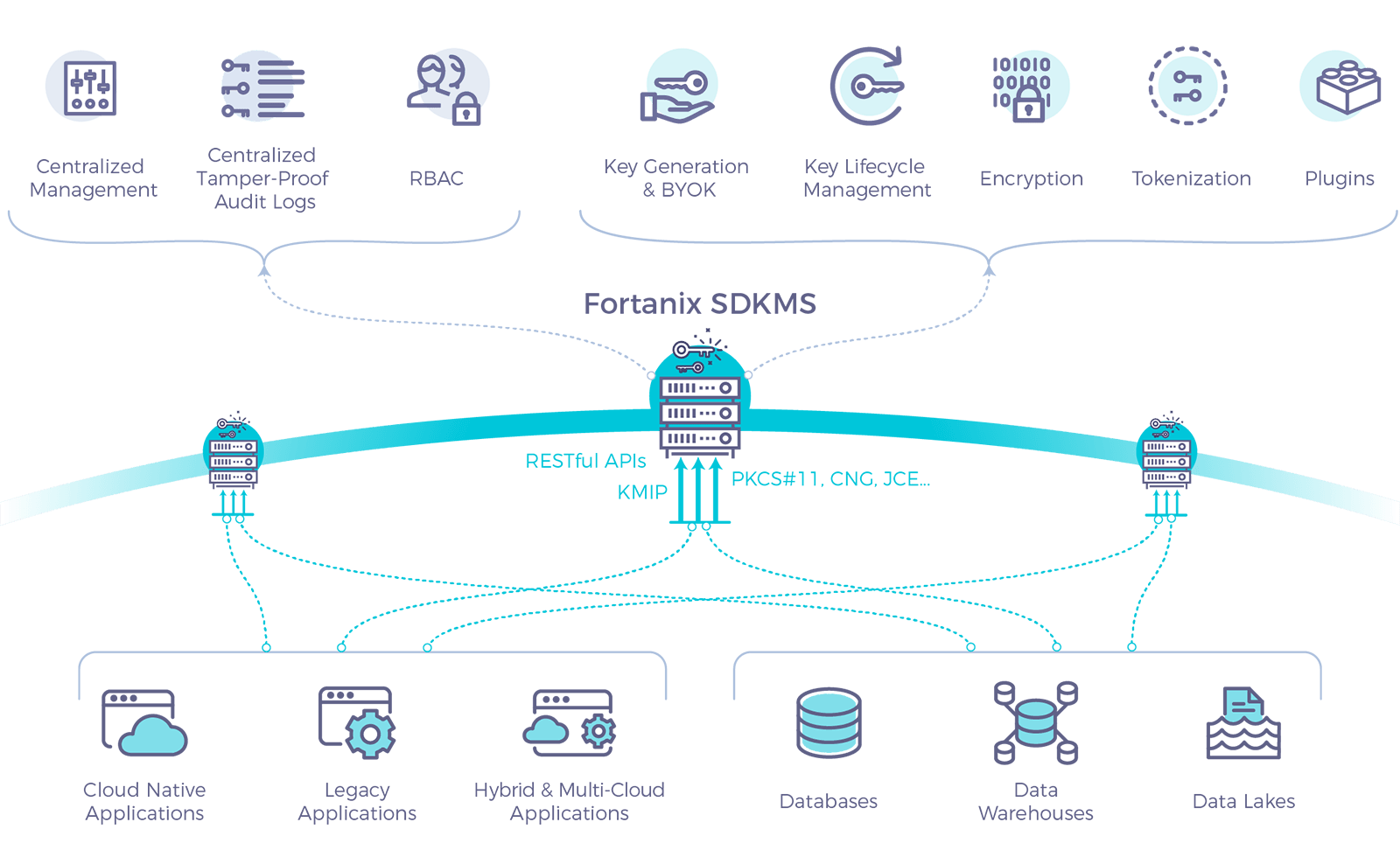
Why can't HSM and key management be provided to you as a managed service? Or can they?.. | by Fortanix | Medium