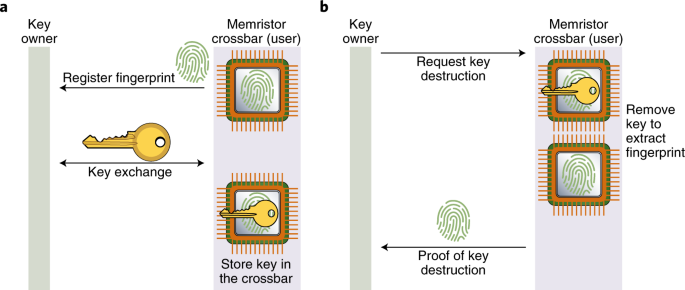
Detailed design of relockable logic locking/unlocking with provable key... | Download Scientific Diagram
Fractured pixelated key vector icon with destruction effect, and original vector image. Pixel destruction effect for key demonstrates speed and movement of cyberspace abstractions. Stock Vector | Adobe Stock



![Infernal Machine: How to get Key of Destruction - X360 Diablo 3 [1080p HD] - YouTube Infernal Machine: How to get Key of Destruction - X360 Diablo 3 [1080p HD] - YouTube](https://i.ytimg.com/vi/GJnBKEt9q5A/sddefault.jpg)